Usability Of Wireless Tools Mikrotik
Explanation of the use of Wireless Tools-Mikrotik Mikrotik Router has Wireless functionality and features that we can take advantage of for communication between devices with Mikrotik wireless communication using the media. But not all Mikrotik Wireless feature can use this, because not all types of Mikrotik is no Wireless Card.
 |
| Usability Of Wireless Tools Mikrotik |
Call it Mikrotik RB 750 who only got 5 ethernet interface and without the wireless interface because there is no wireless card. Specific to Mikrotik Pool, most could use Wireless because it features a Mini PCI slot is available for the wireless card.
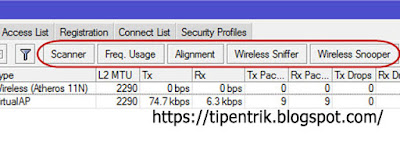
OK, this time we will learn wireless wireless usage i.e. Mikrotik tools standard Mikrotik. Wireless tools is very important in building wireless networks with mikrotik, to monitor and monitor the condition of the wireless network around the US.
To use the wireless tools, you can use the winbox and into the Wireless menu.
There are several tools on mikrotik Wireless with different function, namely: scanners, Frequency Usage Snooper, Align, and Sniffer. Here's an explanation of each wireless tool:
Scanner Tool Mikrotik
True to its name, the scanner function to perform a scan with shows which Access point active around the device. The scanner will display information from the AP about the Mikrotik in detail starting from Mac Address, SSID, Band, Defined, SNR, signal, the Radio Name, until his version of RouterOS (Mikrotik devices if). The following is an example of the use of the scanners.
Frequency Usage Tool Mikrotik
This tool serves to do the scanning frequency of the use of the immediate vicinity of the device your mikrotik. Frequency Usage will display a load of each usage frequency are used a lot what lonely users. So that we can determine which frequencies are not too many users to reduce interference.
Snooper Tool Mikrotik
By using the Snooper tool then reveals a huge traffic load and each is defined by a more detailed information. Snooper can display info Access Point, the number of Station and his Client, signals, as well as each of its bandwidth.
Sniffer Tool Mikrotik
A Packet Sniffer is a tool provided in the Arabian Ranches to catch and tap packages running on the network. This tool is very useful for analyzing network traffic.
Comments